Phishing has become a prevalent and dangerous online threat, targeting individuals, businesses, and organizations worldwide. In this guide, we will explore the concept of phishing and discuss effective strategies for protecting against such attacks.
Phishing refers to the fraudulent practice of tricking individuals into revealing sensitive information, such as passwords, credit card numbers, or social security numbers. This is often done through deceptive emails, websites, or instant messages that appear legitimate but are designed to steal personal or financial information.
Imp of phishing protection
Phishing attacks can result in severe consequences, including financial loss, identity theft, and compromised computer systems. Protecting against phishing is crucial to safeguarding personal and organizational security, privacy, and data integrity.

PHISHING ATTACKS AREN’T JUST CONFINED TO EMAIL
The 5 most common types of phishing attack

ACHIEVE PHISHING PROTECTION

Educate your Employees
Security awareness training programs typically include education on phishing protection that teaches users how to spot phishing email and what to do when they encounter an attack.
DNS authentication services
are a powerful form of phishing protection that usesuse DMARC, DKIM and SPF protocols to determine whether an email sent from a certain domain is legitimate or fraudulent.

Email scanning and filtering
Receive provide email protection by scanning every link and every attachment in every email and preventing users from opening them if they are thought to be dangerous.
Benefits of phishing protection
Real-time protection
“Prevention is better than cure” The best type of protection from phishing attacks is proactivity instead of reactivity. While having software that can remove malware is an excellent thing, you don’t want the malware to be there in the first place. With anti-phishing solutions, you’ll get real-time protection in several ways.
Malicious attachment blocking
Phishing protection software will scan Your incoming emails for links and attachments. If they are determined to be malicious, they will be blocked before reaching your inbox. You won't have to worry about false positives because the technology is sophisticated enough to distinguish.
Click protection
Afraid of clicking on the wrong links while online? You don’t have to worry about that anymore. Anti-phishing software will scan each link you click and block it if it is blacklisted. You won't have to worry about removing viruses because they won't get far enough into your network to infect it.
Two-way spoof protection
Display names and email addresses are easily spoofable by cyber criminals. Anti-phishing software can scan your incoming emails and determine whether or not they have been spoofed. On top of that, they can also add extra measures to your email signatures, so it makes it harder for unauthorized people to spoof your organization’s display name or email address.
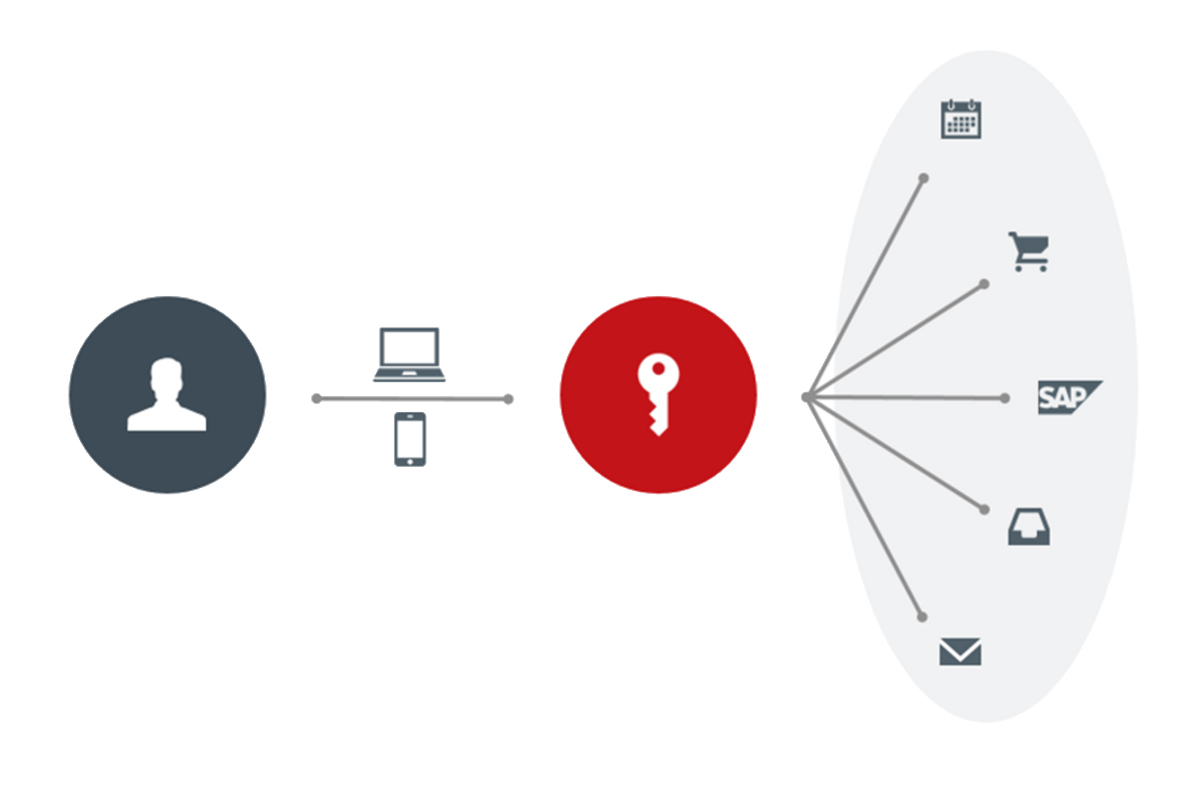
Coverage across all devices
Many anti-phishing techniques focus on protecting computers and laptops, so mobile devices and tablets are frequently overlooked. However, because they connect to the internet, they are just as vulnerable, if not more, than computers. Any reputable and effective anti-phishing company will have software that is cross-platform compatible. That way, you’ll have strong defenses no matter what device you’re on.
PHISHING PROTECTION SOLVES MOST OF YOUR PROBLEMS
Website Security is a measure taken proactively to secure websites against various malwares and attacks. We offer website security. solluction

Protect against zero-day attacks & complex threats with advanced malware detection engines.

See real-time insights into all outbound traffic, threat events, and more — on one dashboard.

Enforce your company policy. Make sure all employees comply by blocking certain domains.

Identify and block unsanctioned applications based on risk score or limit application features.
frequently asked questions
- Phishing protection refers to security measures that companies can take to prevent phishing attacks on their employees. Phishing is a form of cybercrime where attackers dupe targets into revealing sensitive data: bank account numbers, credit card information, login credentials, Social Security numbers and other personally identifiable information.
- Certain anti-phishing protection may block email containing phishing attacks from entering a company's email system at all. Other anti-phishing protection measures can block users from clicking on links and attachments within an email they have received that might be dangerous.
- Anti-spyware and firewall settings should be used to prevent phishing attacks and users should update the programs regularly. Firewall protection prevents access to malicious files by blocking the attacks. Antivirus software scans every file which comes through the Internet to your computer.
- While phishing attacks can be dangerous, not all phishing attacks result in identity theft, malware downloads, network intrusions or other personally petrifying, career-ending, and business razing consequences